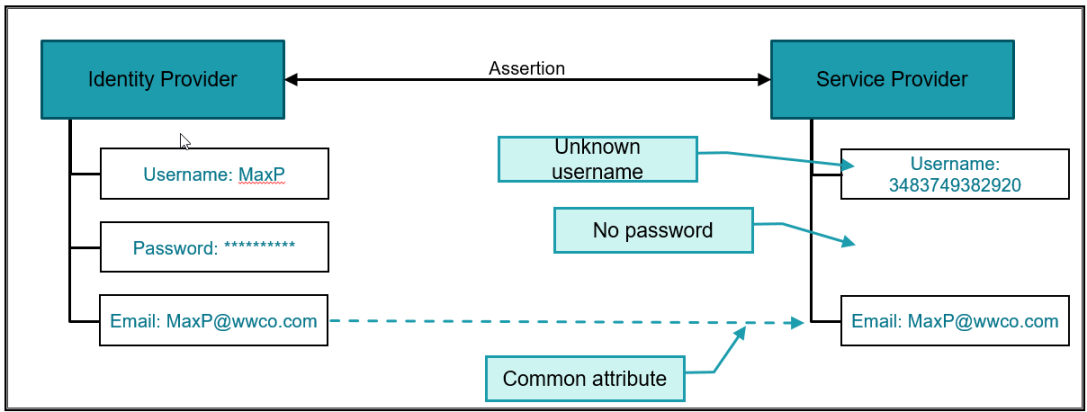
A secret handshake or an inside joke. Fun ways for us to share information to each other, secretly. Without the historical association, others will fail to get access or understand the full meaning. Welcome to SAML SAML is a way to securely share authentication and authorization information between two parties. Most often, SAML is used… Continue reading A Intro to SAML
Tag: saml
Authentication: Your Identity
Most of us ignore authentication because it is seamless with us using our Active Directory username to log onto a domain-joined Windows 10 PC. But when we expand beyond Windows, there are so many other things to consider. I avoided learning about authentication for a long time. So many technologies. So many acronyms. So many… Continue reading Authentication: Your Identity
Access Control
Things I’ve heard (Unfortunately, these are true) I have a hundred or more passwords (I think most of us are in that boat) I still have access to my former employer’s web apps even though I left over a year ago. Let me show you. (Wow, but I’ve seen similar things) I hear layoffs are… Continue reading Access Control