The latest Visio stencils for the Citrix Workspace, including Virtual Apps (XenApp), Virtual Desktops (XenDesktop), Citrix ADC (NetScaler), Endpoint Management (XenMobile), Citrix Hypervisor (XenServer), Content Collaboration (ShareFile) and Citrix Cloud. Citrix Visio 2013-2016 Stencils Citrix Visio 2003-2010 Stencils Citrix PowerPoint 2016 Icons Daniel (Follow on Twitter @djfeller) Change Log October 24, 2022 Visio Updated -… Continue reading Citrix Workspace Visio Stencils
Tag: NetScaler
Integrate NetScaler with XenApp, XenDesktop and XenMobile
In part 1, I created certificates for my environment with Microsoft Certification Authority In part 2, I integrated XenMobile into my XenApp and XenDesktop environment In part 3, I will provide secure remote access to XenMobile, XenApp and XenDesktop with NetScaler. NetScaler and XenMobile In a browser, navigate to http://172.16.0.14. Go to the Configuration screen… Continue reading Integrate NetScaler with XenApp, XenDesktop and XenMobile
Microsoft Certificate Authority for XenApp, XenDesktop, XenMobile and NetScaler
My lab is very XenApp and XenDesktop focused, but I need to expand the functionality to include secure access with NetScaler Gateway and incorporate mobile device management/mobile app management (MDM/MAM) with XenMobile. From what I understand, in order to do this, I really need to install certificates. D’oh! Every time I have to deal with… Continue reading Microsoft Certificate Authority for XenApp, XenDesktop, XenMobile and NetScaler
More to Availability than Live Migration
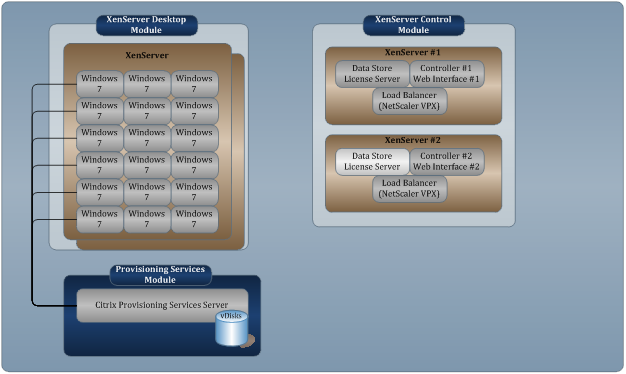
Anytime I’m in a discussion that deals with server or desktop virtualization, the topic usually heads to high availability. I usually get asked about live migration features like XenMotion. Honestly, there are many scenarios where it doesn’t make sense, but that is a discussion for later. What does matter is that your implementation continues to… Continue reading More to Availability than Live Migration
SAN, VDI and SMB
One of the big questions regarding virtual desktops is storage. In fact, I’ve discussed this numerous times (here and here and here). This has mostly been with a focus on IOPS. This time I want to focus on the high-availability aspect you get with shared storage, but with the focus of being on the SMB/SME… Continue reading SAN, VDI and SMB
Danger, Danger My Server Crashed
We all know the impact a server failure can have on a group of users, but what if that server was a core component of a desktop virtualization solution? That’s a lot of unhappy users. Before desktop virtualization, nobody gave a second thought about desktop availability. If a desktop failed, it only impacted a single user… Continue reading Danger, Danger My Server Crashed