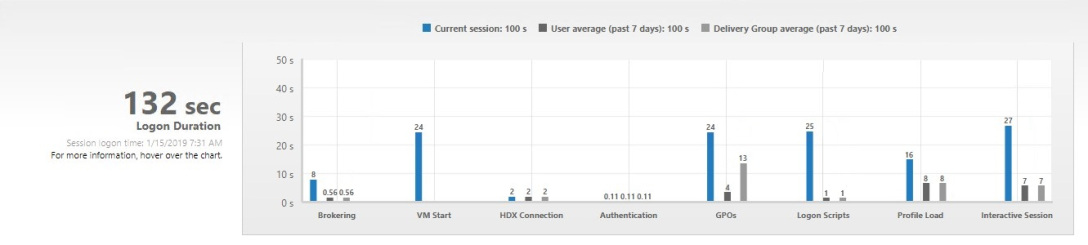
Diagnosing long logon times is quite a challenge. Citrix Director breaks our logon time down into unique phase to help focus your attention on an aspect of the entire logon process instead of logon in its entirety. Looking at my 100+ second logon time, I noticed I have a 24 second virtual machine start time. … Continue reading Logon: VM Start
Tag: xendesktop
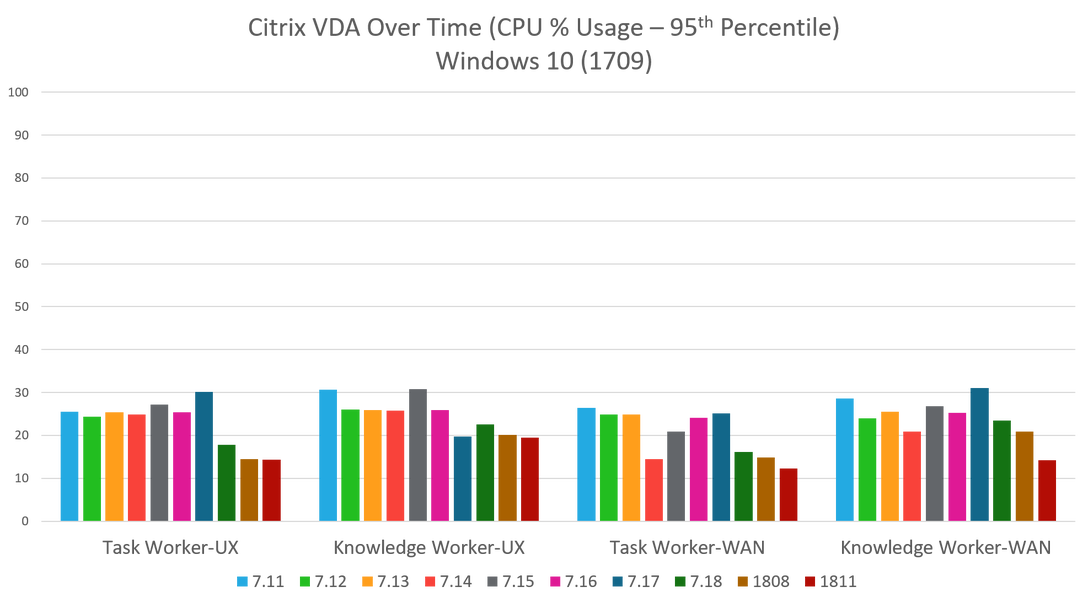
Citrix VDA Performance
Winter in Minnesota. Back the car out of my driveway, reach the road and my car immediately slides, sideways downhill. I think I need new tires. One of the best practices I like to talk about is “Maintain, because set and forget does not work.” We all know it is important to maintain our systems,… Continue reading Citrix VDA Performance
Logon: Brokering
I just experienced a 100+ second logon time for my Virtual Apps and Desktops session. Hopefully, you are not thinking “That’s pretty fast”. If I look at the detailed breakdown of my logon time, you can see it is a mess. Something is happening with my environment to cause things to spike. I want to… Continue reading Logon: Brokering
Synchronize vs Mirror
This has confused me with Citrix Profile Management… What is the difference between synchronizing a folder and mirroring a folder? When I say source and destination, I mean the following: Source = virtual desktop Destination = profile store The descriptions for both sound very similar, so I thought I would dig into this a little… Continue reading Synchronize vs Mirror
Workspace app with StoreFront
You might have heard that the next version of Citrix Receiver is Citrix Workspace app. Workspace app extends the capabilities of Receiver to incorporate other on-premises and cloud-hosted services, like Virtual Apps and Desktops (traditional, on-premises deployment) Virtual Apps and Desktops Service Access Control Content Collaboration Endpoint Management Because Citrix Workspace incorporates more than Windows/Linux… Continue reading Workspace app with StoreFront
LoginVSI PowerShell – Automate Tests
I have a PowerShell function that preps my lab and another executes a single LoginVSI test. Now, I need to fully automate my LoginVSI testing to perform multiple tests without any interaction. I need to do the following: Perform a test for each Master VM I specify For each Master VM, test specific workloads For… Continue reading LoginVSI PowerShell – Automate Tests
LoginVSI PowerShell – New-CitrixVSITest
Being able to automate a LoginVSI test saves a lot of time, but there is more to testing than just the LoginVSI portion. We must remember to get the environment prepared for a LoginVSI test. For a Citrix XenApp and XenDesktop test, I always need to do the following: Prepare environment Remove the first VM… Continue reading LoginVSI PowerShell – New-CitrixVSITest
LoginVSI PowerShell – Invoke-VSITest
LoginVSI automates performance testing and I need to automate LoginVSI. By calling this one function, I can invoke a single LoginVSI test. At a high-level, the test does the following Prepare test These items simply get the environment ready for a LoginVSI test. It includes doing the following: Delete any old test files on the… Continue reading LoginVSI PowerShell – Invoke-VSITest
Pooled Desktops with Local Host Cache
Local host cache, within XenApp and XenDesktop, utilizes a local DB to store configuration information. This local DB is continuously updated by the master SQL DB. When connectivity to the SQL DB fails, the controller automatically switches to the local DB. When the link to the SQL DB is restored, the controller automatically switches back.… Continue reading Pooled Desktops with Local Host Cache
XenApp and XenDesktop PowerShell – Update MCS Image
If you need to automate the updating of a Machine Creation Services machine catalog, this script will be useful. It was created for a XenServer host. The first part is to setup my parameters. For the variables $StorageResource and $HostResource, you will use the names from Citrix Studio – Configuration – Hosting. I use “XenServer”… Continue reading XenApp and XenDesktop PowerShell – Update MCS Image